↳https://criticalengineering.org/projects/vending-private-network/ ( site )
↳https://julianoliver.com/projects/vending-private-network/ ( JOliver )
à propos de Vending Private Network VPN
In this talk, @Danja_Vasiliev gives an overview of "dark internet topologies" in the context of the commissioned piece //Vending Private Network// he did together with @Julian_Oliver ( 2018 )
Conf
Cite cette carte des câbles sous-marins :
https://www.submarinecablemap.com
Are.na ( adhoc_mesh_ntwrk )
https://www.are.na/vincent-bonnefille/adhoc_mesh_ntwrk
Membre du https://criticalengineering.org
@The_Critical_Engineering_Working_Group
2022 EDIT
- Submarine Cable Map 2015
https://submarine-cable-map-2015.telegeography.com/ - Traceroute mapper ( tool git )
https://stefansundin.github.io/traceroute-mapper/?trace=traceroute%20to%2083.118.202.51%20(83.118.202.51)%2C%2030%20hops%20max%2C%2060%20byte%20packets%0A%201%20%20livebox.home%20(192.168.1.1)%20%204.040%20ms%0A%202%20%2080.10.253.25%20(80.10.253.25)%20%209.688%20ms%0A%203%20%20*%0A%204%20%20*%0A%205%20%20ae51-0.nridf101.rbci.orange.net%20(193.252.98.94)%20%2012.098%20ms%0A%206%20%20*%0A%207%20%20*%0A%208%20%20*%0A%209%20%20*%0A10%20%20*%0A11%20%20*%0A12%20%20*%0A13%20%20*%0A14%20%20*%0A15%20%20*%0A16%20%20*%0A17%20%20*%0A18%20%20*%0A19%20%20*%0A20%20%2051.202.118.83.in-addr.arpa.celeste.fr%20(83.118.202.51)%20%2010.492%20ms%0A - History souces

Via The Critical Engineering Working Group Berlin, October 2011-2019
JavaScript is dangerous! Why? How are websites vulnerable to it? Find out about bug-bounties from @Tom_Scott
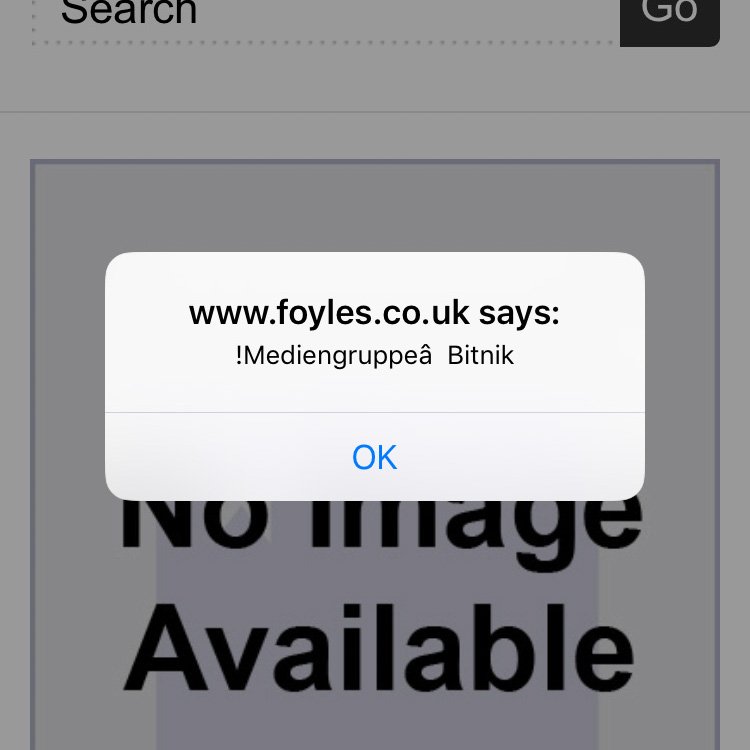
Scammers have taken an old browser scam and invigorated it using a clever and new tactic that takes advantage of your web browser's full-screen mode to show a fake Windows 10 desktop stating your computer is locked.
This type of scam is called a police browser locker. which pretends to be law enforcement locking your browser because due to illegal activity. These scams then state that if you pay a fine via a credit card, it will unlock your computer so you can use it again.
The menu ::
Egg and bacon
Egg, sausage and bacon
Egg and spam
Egg, bacon and spam
Egg, bacon, sausage and spam
Spam, bacon, sausage and spam
Spam, egg, spam, spam, bacon and spam
Spam, spam, spam, egg, and spam
Spam, spam, spam, spam, spam, spam, baked beans, spam, spam, spam and spam
Lobster thermidor aux crevettes with a Mornay sauce garnished with truffle pâté, brandy and with a fried egg on top and spam
Spam, sausage, spam, spam, spam, bacon, spam, tomato and spam (this is only in the LP version's menu, but the TV version features the Hungarian trying to order it)
[ "Spam" is the twenty-fifth episode of Monty Python's Flying Circus. ]
[ {{ "Spam is the last sketch } of the "Spam" épisode } ]
Best définition online (vo) :
https://www.dailymotion.com/video/x5v0vml
Leaks of datas
HTTPS , HSTS ,
Referrer Policy ,
Content Security Policy ( CSP )
...
Check security on your website
From : https://neustadt.fr/essays/against-a-user-hostile-web/